这套GitHub 1300星的NLP课程即将完结,视频授课,在线答疑丨课程
郭一璞 发自 椰子树下
量子位 报道 | 公众号 QbitAI
最近NLP方向的资源越来越多,GitHub上又出现了一套新的课程,目前已经获得了1300多颗星星。
在这套NLP课程中,作者们把这套课程拆分成了13周,从文本嵌入分类开始讲,到Seq2Seq,再到机器翻译、对话系统,内容丰富。
每周的课程除了主要的讲座视频之外,还有研讨会部分,听众可以在研讨会上用英文提问,已经讲完的课程带有视频和Python笔记,另外还有课后作业笔记。
13周的课程
具体的课程时间表如下:
第一周
讲座:介绍文本嵌入、分布式语义、LSA、Word2Vec、GloVe的用法和使用场景。
研讨会:单词和句子嵌入。
第二周
讲座:文本分类。
文本表示的经典方法:BOW,TF-IDF。
神经方法:嵌入,卷积,RNN。
研讨会:卷积神经网络的薪酬预测; 解释网络预测。
第三周
讲座:语言模型,N-gram和神经方法; 可视化训练的模型。
研讨会:使用语言模型生成ArXiv论文。
第四周
讲座:
Seq2seq:编码器 - 解码器框架。
Attention:Bahdanau模型。
研讨会:酒店和宿舍描述的机器翻译。
第五周
讲座:结构化学习,结构化感知器,结构化预测,RL基础知识。
研讨会:POS标签。
第六周
讲座:期望最大化和单词对齐模型。
研讨会:实现期望最大化。
第七周
讲座:机器翻译,回顾PBMT的主要思想,过去3年NMT开发的应用程序特定思想以及该领域的一些开放性问题。
研讨会:学生演讲。
第八周
讲座:网络学习的内容和原因:“模型”永远不仅仅是“模型”!NLP中的多任务学习,如何理解,模型表示包含哪些信息。
研讨会:通过与其他任务共同学习,提高指定实体的认可度
第9~13周
第9~13周的内容作者们还没有更新,根据目录来看,主要是讲域名适应、对话系统、对抗方法和TBA。
作者
这份NLP教程一共有5位作者,其中一作小姐姐Elena Voita是俄罗斯AI公司Yandex的研究员,专供NLP、机器翻译方向,今年还发了一篇关于文本识别和机器翻译的ACL论文。
Elena Voita目前在阿姆斯特丹大学读机器学习、NLP方向的博士,同时还是爱丁堡大学访问博士。
传送门
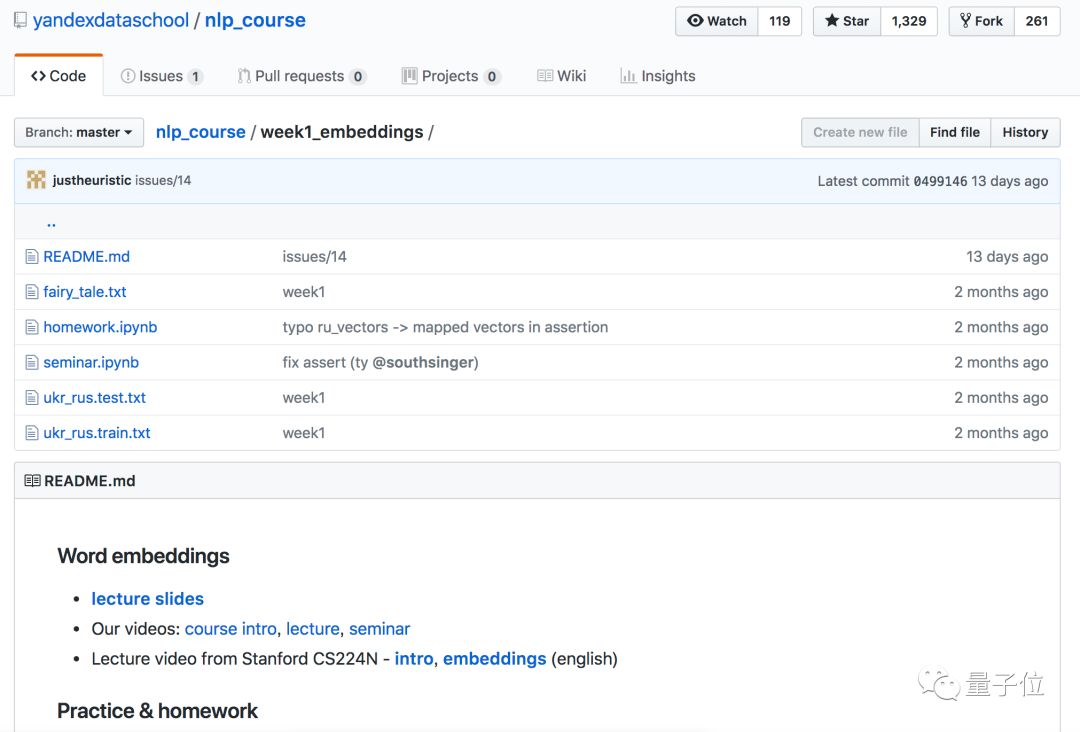
GitHub:
https://github.com/yandexdataschool/nlp_course
Jupyter:
https://mybinder.org/v2/gh/yandexdataschool/nlp_course/master
— 完 —
年度评选申请
加入社群
量子位AI社群开始招募啦,欢迎对AI感兴趣的同学,在量子位公众号(QbitAI)对话界面回复关键字“交流群”,获取入群方式;
此外,量子位专业细分群(自动驾驶、CV、NLP、机器学习等)正在招募,面向正在从事相关领域的工程师及研究人员。
进专业群请在量子位公众号(QbitAI)对话界面回复关键字“专业群”,获取入群方式。(专业群审核较严,敬请谅解)
活动策划招聘
量子位正在招聘活动策划,将负责不同领域维度的线上线下相关活动策划、执行。欢迎聪明靠谱的小伙伴加入,并希望你能有一些活动策划或运营的相关经验。相关细节,请在量子位公众号(QbitAI)对话界面,回复“招聘”两个字。

量子位 QbitAI · 头条号签约作者
վ'ᴗ' ի 追踪AI技术和产品新动态