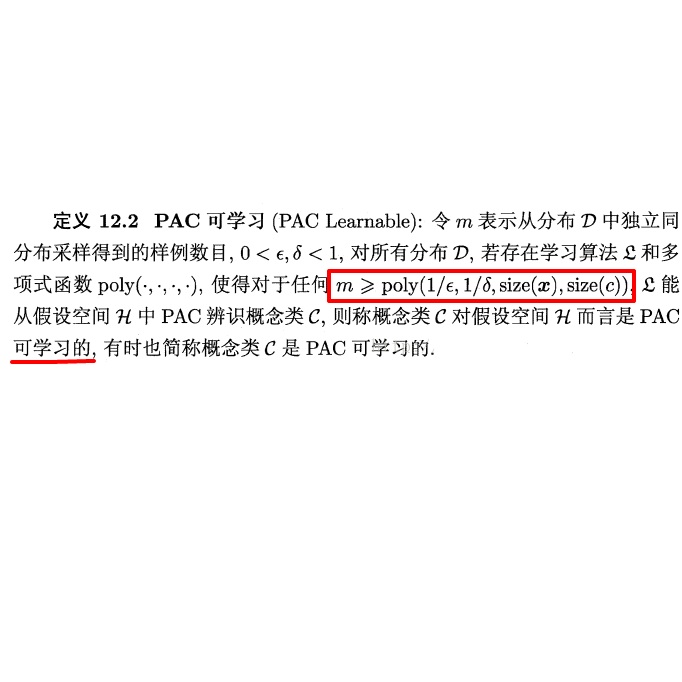
Machine learning-based hardware malware detectors (HMDs) offer a potential game changing advantage in defending systems against malware. However, HMDs suffer from adversarial attacks, can be effectively reverse-engineered and subsequently be evaded, allowing malware to hide from detection. We address this issue by proposing a novel HMDs (Stochastic-HMDs) through approximate computing, which makes HMDs' inference computation-stochastic, thereby making HMDs resilient against adversarial evasion attacks. Specifically, we propose to leverage voltage overscaling to induce stochastic computation in the HMDs model. We show that such a technique makes HMDs more resilient to both black-box adversarial attack scenarios, i.e., reverse-engineering and transferability. Our experimental results demonstrate that Stochastic-HMDs offer effective defense against adversarial attacks along with by-product power savings, without requiring any changes to the hardware/software nor to the HMDs' model, i.e., no retraining or fine tuning is needed. Moreover, based on recent results in probably approximately correct (PAC) learnability theory, we show that Stochastic-HMDs are provably more difficult to reverse engineer.
翻译:机器学习型硬件恶意软件探测器(HMDs)在防范恶意软件系统方面提供了潜在的游戏变换优势。然而,HMDs遭受对抗性攻击,可以有效地反向设计,然后躲避,让恶意软件躲避。我们通过粗略计算提出新的HMDs(Stochatic-HMDs)来解决这个问题,使HMDs的推论计算和随机分析,从而使得HMDs具有抵御对抗性规避攻击的适应力。具体地说,我们提议利用电压过压来诱导HMDs模型的随机计算。我们表明,这种技术使HMDs更能适应黑盒对抗性对抗性攻击情景,即反向工程和可转移性。我们的实验结果表明,Stochacast-HMDs提供了有效的防御性攻击,同时避免副产品节能,而无需对硬件/软件或HMDs模型作任何改动,即不需要再培训或微调。此外,根据近期的结果,我们也许更难的Stochably理论显示,我们更难的Stovicaltical-mical-mi变校。